So I had it going for a couple weeks without any issues, until the morning I decided to check out my network traffic. I saw some odd stuff in my firewall logs that didn't make sense, and they were coming from the QNAP system. It started because I saw a good deal of inbound UDP traffic being blocked. UDP is basically TCP's bastard cousin. It is not typical for legitimate internet services to use UDP. So I checked out some IP addresses and they were coming from the usual oversees locations. No big thing, most likely internet scanning on UDP to see if anyone's firewall will allow it through. So I continue through the log and notice outbound UDP traffic. I panic a little and then notice it is going out over 6881. Now my lovely firewall allows me to do an on-demand packet capture, which is handy as it sits between my LAN and Internet, so it can see everything. So I ran the capture and then filtered the results in Wireshark:
Notice the many different non-US destinations? Yeah that didn't sit right with me. Did some digging as I have not memorized all my TCP/UDP port numbers and found that this is typical of BitTorrent listeners. I did some additional searching and found that the QNAP has a Download Manager service that comes turned on by default. This download manager runs like a Torrent listener so this is beacon traffic to the torrent network. I took a look at some of the packets and found it to be random garbage, nothing malicious. But still, that is traffic I don't want going out without my permission, least of all to overseas locations. I made some changes on the firewall that would automatically block traffic based on country of origin and found a nifty forum post about disabling the feature and hardening the device further.
- Disable Download Station - unless you can find a good use for it. This can be done from "My Apps." Just slide the bar to the left.
- Now we need some clean-up. We will need to make sure only authorized networks can access the QNAP. Go to the Security Settings in the QNAP control panel.
- In the Security Settings, you will want to select "Allow connections from the list only." Then add the internal IP address/ranges you wish to allow to access the device. This is handy if you happen to have a guest wireless network that may touch your main network. Again who would have that, it is just silly. Refer to the image below, IP addresses are obfuscated, but those would change based on the network anyway. I did have to add my VPN IP Pool in as it is different from the internal LAN.
So that is it, piece of cake! Once you make the changes it will restart the network services, so you may lose access to the shares for a minute or 2. After I made those changes the traffic pretty much stopped. I am still getting a bunch of inbound UDP getting blocked but that should decline as well. Anyway hope this is helpful to some folks. The device is pretty useful but again, don't always trust the default settings or apps. Take the time to understand what you plugged into your network! Any questions feel free to leave a comment below!
***UPDATE***
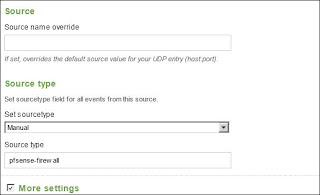
So quick update on the network security... as I sit here waiting for my plane to Louisville for DerbyCon 2013, I decided to test my VPN to the home office. It wouldn't connect, so through other magical means I remoted in a different way to check the systems. Firewall check! It was passing traffic nicely. So logged into the QNAP where the service is hosted and immediately saw the warning indicator for unauthorized network attempting to connect on my VPN port. Nifty, that made fixing the issue pretty easy. Made the necessary changes and all is working now. So if you lock your QNAP down and use the VPN service, you may need to open some ranges or just not use the block networks piece. The VPN is only temporary until I can bring up a new full time server.